Integrate NetMotion Mobility XE VPN
This technical integration guide describes how to integrate a NetMotion Mobility Software and an Identity as a Service Authentication Service account. Although this document specifically covers the NetMotion Mobility Software, the information provided applies to all NetMotion appliances using the Device Manager software. The aim of this integration is to provide strong, second-factor authentication for your NetMotion Mobility Software solution using Identity as a Service.
Note: This integration was tested using Identity as a Service version 5.12 and Netmotion version 11.31.9670. Some configuration steps may differ from the documentation provided or the steps in this integration guide may not be effective (due to Entrust not having tested and validated with the version you are using). For different versions, this integration guide may still offer a standard base to help fast-track SAML authentication setup for your application, but in the event there are issues, contact support@entrust.com for assistance.
This integration was tested using Identity as a Service version 5.12 and Netmotion version 11.31.9670. Some configuration steps may differ from the documentation provided or the steps in this integration guide may not be effective (due to Entrust not having tested and validated with the version you are using). For different versions, this integration guide may still offer a standard base to help fast-track SAML authentication setup for your application, but in the event there are issues, contact support@entrust.com for assistance.
Before you begin, review the following:
Integration informationIntegration information
Partner name: NetMotion
Partner product: NetMotion Mobility XE
Product version: 11.31.9670
Product name: Mobility Client
Product version: 11.32.12223
Supported authentication methodsSupported authentication methods
| Authentication method | Notes | Supported protocols |
| Grid |
Two-step authentication only |
EAP-GTC |
| Token |
One-step or two-step authentication. Note: Challenge/response tokens unsupported with MSCHAPv2. |
EAP-GTC or EAP MSCHAPv2 |
| Temporary Access Code |
|
EAP-GTC |
| OTP (One Time Password) by SMS or Token |
Two-step authentication only |
EAP-GTC or EAP-MSCHAPv2 |
| Knowledge-based authentication |
The RADIUS proxy only supports a single question and answer. For CHAP and MS-CHAP, the answer must be an exact match. Two-step authentication only |
EAP-GTC |
| External (No Password) |
First-factor |
EAP-GTC |
| Password |
First-factor |
EAP-GTC |
| Soft Token push |
Two-step authentication only |
EAP-GTC |
| Mobile Smart Credential push |
Two-step authentication only |
EAP-GTC |
PrerequisitesPrerequisites
Complete the following steps before integrating your authentication system with Identity as a Service:
Install and configure your first-factor authentication resource using the documentation provided by the vendor. The first-factor authentication resource can be a RADIUS server or an external authentication resource (a Local DB, LDAP-compliant directory or Windows domain controller through Kerberos).
Install and configure the RADIUS appliance using the documentation provided by the vendor. The device must be able to route traffic before integrating with Identity as a Service.
Install and configure Identity as a Service and an Identity as a Service Gateway (containing a RADIUS proxy agent). Take note of the shared secrets, IP addresses, and ports you use. You need this information to configure the RADIUS appliance and first-factor authentication resource.
If you want to configure your RADIUS appliance and first-factor authentication resource to recognize Identity as a Service user groups, you must define the Identity as a Service user groups first.
Integrate Netmotion Mobility XE VPN
Complete the following to integrate NetMotion with IDaaS.
Step 1: Configure NetMotion Mobility XE VPNStep 1: Configure NetMotion Mobility XE VPN
The following procedure describes how to configure the NetMotion Mobility XE Authentication settings to use the Identity as a Service Authentication Service. This procedure assumes that you are familiar with the Mobility Console interface.
Configure the NetMotion Mobility XE VPN
Log in to the NetMotion Console. The NetMotion Dashboard page appears.
Click Configure > Authentication Settings. The Authentication Settings page appears.
In the Global Authentication Settings list, select Authentication > Mode.
In the Authentication Mode field, select User authentication only from the drop-down list.
In the Global Authentication Settings list, select Authentication > Protocol.
Under Authentication - Protocol, select RADIUS – EAP (PEAP and EAP-TLS). This is the correct option if you are using EAP GTC or MSCHAP-V2.
Click Apply.
Select Authentication > EAP-GTC > Auto-Response Mode.
Optional: Select the Auto-response mode check box if you want an identical prompt window for challenge authentication or uncheck this box if you want a separate challenge prompt window.
In the Global Authentication Settings list, select Radius > Servers.
In the RADIUS Servers pane, click Add. The RADIUS Server Entry page appears.
In the RADIUS Server Entry page, enter the following information:
Host address: Enter the Identity as a Service account URL.
Port: Enter the port number on which the RADIUS application is configured to listen.
Shared secret: Enter the RADIUS secret.
Confirm Shared secret: Enter the RADIUS secret.
Click OK.
In the Global Authentication Settings list, select Radius > NAS ID.
In the NAS ID field enter the name netmotion or the IP address of the NetMotion server.
Click Apply.
Select Radius > Retransmit Interval.
In the Interval field, enter 40000.
Click Apply.
Step 2: Configure the NetMotion Mobility XE client settingsStep 2: Configure the NetMotion Mobility XE client settings
Configure the NetMotion XE client settings
Login to the NetMotion Console. The Dashboard page appears.
From the top menu, click Configure > Client Settings. The Client Settings page appears.
In the Global Client Settings pane, scroll down until you see the Logon option.
Click Always Prompt for User Credentials.
Select the Always prompt when connecting check box. Click Apply.
Click Connecting Dialog Delay.
In the Delay Time field, enter the maximum time in seconds, for example 120. Click Apply.
Click Connecting Dialog Duration.
In the Wait Time field enter maximum time in seconds, for example 120. Click Apply.
Step 3: Configure the server certificateStep 3: Configure the server certificate
If you are using a server certificate for Identity as a Service, and the NetMotion client is set to validate server certificates, then you must install the self-signed or CA certificate used to issue the SSL server certificate on the NetMotion client machine.
Configure the SSL certificate on the client machine
Export the SSL certificate from the gateway instance on your Identity as a Service account to the client machine. See the procedure to Export SSL certificate in Manage Gateway certificates for more information.
Import the SSL certificate into the local Trusted Root CA store on the NetMotion client machine.
If you do not want to validate the certificate, do the following:
Go to the client machine and open the NetMotion client. The NetMotion Mobility Client page appears.
Click Configuration. The General options page appears.
Select the Server Certificates tab.
Deselect the Validate server certificate box.
Click OK to save the settings.
Step 4: Add NetMotion Mobility XE to Identity as a ServiceStep 4: Add NetMotion Mobility XE to Identity as a Service
Note: If you enable Push Authentication Fallback, you must set the Client Network Failover timeout (a NetMotion Client setting under ‘Timeout’) to a value greater than the Push Authentication Fallback Timeout.
Note: Entrust recommends that when multiple RADIUS applications are configured that each RADIUS application is given a unique shared secret.
Integrate a RADIUS client
Click ![]() > Security > Applications. The Applications page appears.
> Security > Applications. The Applications page appears.
Click Add. The Select an Application Template page appears.
Do one of the following:
Select RADIUS and VPN Integrations from the search drop-down list and scroll to find the application you want to add to IDaaS.
- or -
In the Search bar, enter a search option to filter for the application you want to add to IDaaS.
Click Netmotion. The Add Netmotion page appears.
Optional: Edit the Application Name.
Optional. Enter a Description for your application.
Optional. Add a custom application logo as follows:
Click ![]() next to Application Logo. The Upload Logo dialog box appears.
next to Application Logo. The Upload Logo dialog box appears.
Click ![]() to select an image file to upload.
to select an image file to upload.
Browse to select your file and click Open. The Upload Logo dialog box displays your selected image.
If required, resize your image.
Click OK.
Click Next. The Setup page appears.
Click Add to next to Hosts to add the host name of the VPN server. The RADIUS agent receives the request on this host. The RADIUS Agent on the Gateway determines the RADIUS application the request is for based on the host name and port.
Enter the host name in the Host dialog box and then click OK. Repeat this step to add more host names.
In the Port field, enter the port on which the RADIUS agent accepts messages.
Tip: Do not enter 8443 as the port number for this application. Port 8443 is used by the Entrust Identity Enterprise agent in your Gateway.
Attention: The RADIUS agent uses the host name that sent a request and the port number that it received the request from to determine which RADIUS application made the request. Because of that:
–Two RADIUS applications with the same port value cannot share any host names.
–Two RADIUS applications that have one or more matching host names must have different port values.
In the Shared Secret field, enter the shared secret that is used by your VPN server. This is the RADIUS secret shared between your VPN server and the RADIUS server. The shared secret value must match a shared secret in your RADIUS client.
From the Select RADIUS Agent drop-down list, select the name of the Gateway containing the RADIUS agent to which this application will be assigned.
Optional: From the Select RADIUS Attribute for IP Address drop-down list, select the RADIUS attribute that corresponds to your IP location.
In the Challenge Response Queue Max Time field, set the number of seconds that the RADIUS agent waits for a response to first-factor authentication. The default value is 180 seconds.
In the Challenge Response Queue Max Size field, set the maximum number of second-factor challenge requests allowed in the queue of your RADIUS application. The default value is 1000 requests. The maximum value is 10,000.
In the Request Cache Timeout field, set the number of seconds to cache requests. The default value is 10 seconds.
From the Character Set drop-down list, select the character set used to decode and encode string values (including the user ID and password values) in RADIUS messages. The options are UTF-8 and ISO-8859-1.
Optional: Select Log RADIUS messages to enable RADIUS message logging. When enabled, messages for the RADIUS agent are logged to the same log file as the gateway logs.
Optional: Enable the Authentication Settings.Optional: Enable the Authentication Settings.
Select Enable Push Authentication Fallback if you want to authentication to fallback to another authenticator in the event of a failure. If required, set the Push Authentication Fallback Timeout to the number of minutes before the push authentication times out.
Select When authenticating the user will be asked to select their second-factor authenticator. When selected, after the user responds to the first-factor challenge, they are prompted to select their second-factor authenticator. The list of available second-factor authenticators is set by the resource rule.
The following is a list of supported strings matched to the authentication types:
Grid: grid
Knowledge-based Authentication: kba
One-time password: email, sms, voice
Smart Credential Push: scpush
Temporary Access Code: tac
Token: token
Token push: push
Select Indicate if requests must include the message-authenticator attribute for incoming messages to include the message-authenticator attribute for incoming messages.
Select Indicate if requests must include the message-authenticator attribute for outgoing messages to include the message-authenticator attribute for outgoing messages.
Select Remove domain from user ID for incoming requests to remove the domain value from the user ID during authentication when the user ID provided by the RADIUS client is in the format domain\username and the user ID in IDaaS is in the format username.
Select Indicate if Active Directory password authentication requests are handled by the same Gateway Instance that initiated the request to require that Active Directory password authentication and change requests that are initiated as part of the RADIUS authentication are handled by any Gateway Instance in the same Gateway cluster that initiated it. If disabled, the request is handled by any Gateway Instance.
Select Enable one-step multi-factor authentication. When enabled, the user enters their user ID and then their password and token response in the password field. If you select this option, second factor authenticators available in the resource rule are limited to token and temporary access code.
Enter the One-step multi-factor authentication security token length. This is the length of the token or temporary access code response if you enable one-step multi-factor authentication.
Optional. Add Response Attributes.Optional. Add Response Attributes. Response attributes are returned to the RADIUS application after successful authentication. Use this setting to configure RADIUS attributes to return information such as the user's group information to the VPN server.
When adding response attributes, you optionally add group filters. For example:
Example:
Users in IDaaS may belong to one of the following groups CANADA, US, UK, FRANCE.
The VPN server wants the FilterID attribute returned from the IDaaS RADIUS agent to be the value NA or EUROPE, depending on whether the user is in NA (Canada, US) or Europe (UK, France).
To do this, use a RADIUS attribute filter for the FilterID attribute with a Groups value with the following filters:
- match CANADA, replace NA
- match US, replace NA
- match UK, replace EUROPE
- match FRANCE, replace EUROPE
Set the Response Attributes as follows:
Click ![]() Add. The Add a Response Attribute dialog box appears.
Add. The Add a Response Attribute dialog box appears.
Select the RADIUS Attribute ID from the drop-down list. The option you select depends on your VPN vendor.
Select the Value Type from the drop-down list.
To return a static value specific in the RADIUS attribute definition, select Static and enter a Value in the field and then click Add.
To return the user’s group membership, select Group and then optionally do the following:
- Click Add to add filters.
- Enter the Match and the Replace attribute filters.
- Click Add to add more attribute filters.
- If you add multiple filters, you can drag and drop them in order of preference.
- Select Stop after matching filter if you only want one the filter to return one value. Using the example above, if you want NA to have preference over Europe, make sure to list Canada and US in the list of filters.
- For Multiple Values Per Attribute, enter the Value Separator and then click Add.
Note: If a user belongs to more than one group, you can either add a separate attribute to your RADIUS response for each group or you can combine all of the groups into a single attribute. For example, if the user belongs to G1,G2,G3 then you would
- return a RADIUS response with three attributes
OR
- return a RADIUS response with one attribute and a value like “G1,G2,G3” where the , is defined in the Value Separator setting or a value like “G1 G2 G3” where the Value Separator is defined as a space.
Attention: The default group separator is a space. If you have group names that are separated by a space, use another separator, such as a comma.
Repeat these steps to add more response attributes.
Optional: Configure the EAP Settings to set up the application to use the EAP RADIUS authentication protocol.
Select EAP Enabled to allow the RADIUS application to accept EAP messages.
When enabled, authentication messages with EAP content are treated as EAP requests. The application can accept only EAP authentication requests.
When disabled, incoming authentication requests are processed by the RADIUS application as a standard RADIUS authentication request (even if the request includes EAP content). In this case, the application can accept only standard RADIUS authentication requests.
Select the EAP Protocol from the drop-down list. The options are PEAPv0 with MS-CHAPv2 and PEAPv1 with GTC.
This setting defines the type of EAP authentication protocol that is performed on EAP requests received by the RADIUS application. Consult the configuration requirements of your VPN server to determine which EAP protocol to select.
Select Return MPPE Keys to include the MPPE (Microsoft Point-to-Point Encryption) recv and mppe send keys in the Access-Accept message returned during a successful EAP authentication. The setting is enabled by default.
Select Use PEAPv1 label when calculating MPPE Keys to use the PEAPv1 label when calculating the mmpe recv and mppe send keys.
Leave the Minimum TLS Version, Maximum TLS Version and Allow Weak Ciphers at the default settings unless you have an older VPN and need to configure these settings to allow older versions of TLS or weaker ciphers to interoperate with older VPN servers that do not support the latest versions.
Configure the Deprecated Settings if your RADIUS application is connected to a Gateway version older than 3.0. These values are only required for backwards compatibility.
Select Token OTP Only, Password with second-factor, or No first-factor as the Authentication Type. This setting defines the level of authentication required to access a RADIUS application that relies on a gateway RADIUS agent configured before release 3.1.
Note: MSCHAPv2 authentication is not supported when No first-factor authentication is configured for the RADIUS application.
Click Submit.
Step 5: Add a resource ruleStep 5: Add a resource rule
Step 6: Test the integration
Note: You can test the NetMotion integration using single-factor authentication with AD password and Token response or using two-factor authentication. Before testing the integration, select the Auto-response option in your NetMotion server settings.
Press Control+Alt+Delete, and log in to the Windows computer using your regular domain credentials.
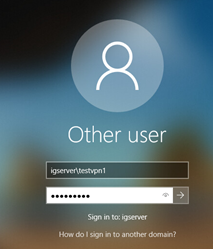
Enter your domain user name and Identity as a Service token response..
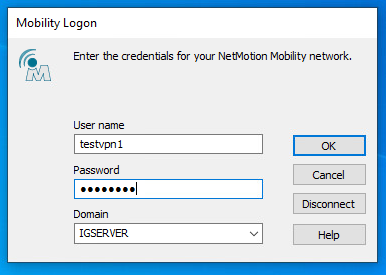
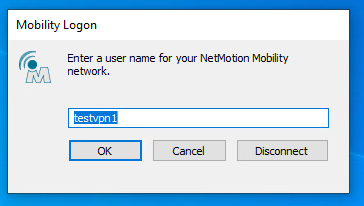
When prompted for the Mobility Login credentials, enter the details as follows:
For the User name, enter the Identity as a Service user name with domain name.
For the Password, enter the token response from one of the tokens registered to the Identity as a Service user.
Click OK.
Note: Ensure that you have selected Auto-response as described in Configure NetMotion Mobility XE VPN.
Test two-factor authenticationTest two-factor authentication
Press Control+Alt+Delete, and log in to the Windows computer using your regular domain credentials.
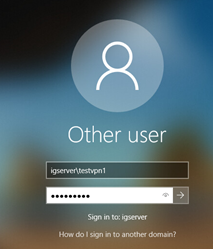
Enter the Identity as a Service user name and password.
Click OK.
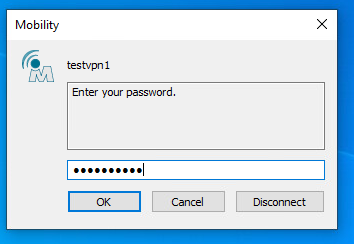
Enter a response to the next challenge that is presented (for example, a grid response).
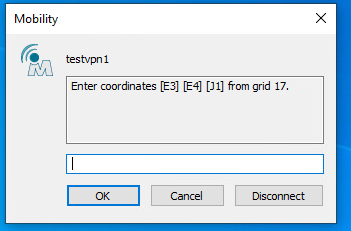
Click OK.